Semi-Invasive IC Extraction is not the whole renew technology, and it is very easy to proceed the electrical magnetic analysis on the naked IC. We can still recall the good old days of protective mcu extraction when the IC package being decapsulated, microcontroller IC memorizer protection bit exposed under the ultra-violet light and extraction old IC with EEPROM basement. Semi-invasive chip extraction can use below method: Ultra-violet radiation, X ray, laser, electrical magnetic and heat. These methods can be used in single ways or use them in the combination for microcontroller code extraction.
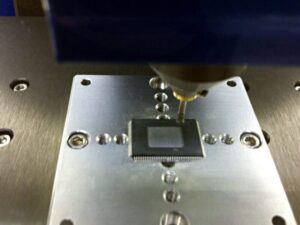
Use cheap and simple facility can proceed the swift and strong microcontroller code extraction, these extractions use computer controller workstation to proceed the automatically operation, and can complete the microcontroller extraction process within several hours which the invasive MCU extraction will normally require days or even weeks.
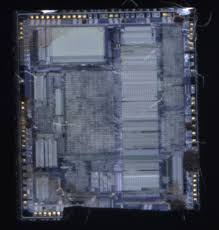
Semi-invasive IC extraction is not considered a whole new technology, but rather an evolution of older hardware-level attack techniques used against secured microcontroller and microprocessor devices. It does not always require the most sophisticated laboratory equipment, which makes it more accessible to research teams or reverse engineers. By removing or thinning the chip package to expose the silicon surface without making direct electrical contact, analysts gain a “window” into the memory architecture of the device. This allows different methods of interference or observation to be applied in order to bypass the locked, protected, or encrypted firmware regions.
In the past, during the so-called “good old days” of protective MCU extraction, the IC package could be decapsulated, and the EEPROM basement or flash protection bits were exposed under ultraviolet radiation. By carefully controlling the light dosage, engineers could flip the security fuse, thereby unlocking the hidden program or binary contents. Although such methods are less common today due to improved security structures, the principle of weakening or altering protection bits using physical or energy-based methods still applies.
Semi-invasive chip extraction typically employs one or more of the following attack vectors:
-
Ultraviolet Radiation – Direct exposure to UV light can reset or weaken fuse bits, especially in older EEPROM-based devices, enabling partial firmware dump operations.
-
X-ray Imaging – Provides visibility into structural layers and sometimes can be exploited to determine memory patterns or to degrade specific protective layers.
-
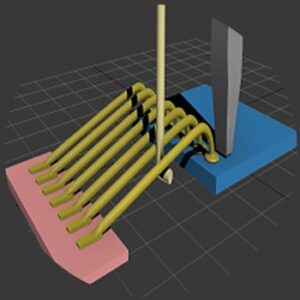
Laser Attacks – Highly localized beams can alter transistor states, inject faults, or bypass security during boot-up sequences.
-
Electromagnetic Analysis – Observing EM radiation leakage during program execution makes it possible to decode instructions or extract heximal data from secured memory.
-
Thermal and Heat Injection – Controlling temperature at the die level can destabilize security logic or allow temporary access to protected firmware regions.
One of the key advantages of semi-invasive techniques is that they can be combined. For example, applying electromagnetic fault injection together with laser targeting may provide a greater chance of breaking through advanced security than using either method alone. These approaches are considered more refined than brute-force electrical probing, yet less destructive than full invasive reverse engineering.
The difficulties lie in maintaining control and precision. Even though semi-invasive methods avoid directly wiring into the silicon substrate, they still require clean-room environments, high-resolution microscopes, and specialized instruments. Misalignment of a laser pulse or overheating of the die can permanently damage the chip, making any chance of recovery or restoration impossible. Furthermore, modern secured MCUs integrate sensors that detect abnormal environmental conditions such as excessive light, temperature shifts, or electromagnetic anomalies, shutting down or erasing the flash contents when an attack is suspected.
Nevertheless, when successful, semi-invasive reverse engineering provides an effective way to clone, replicate, or duplicate legacy devices, ensuring continuity for industries that rely on discontinued microcontrollers. It remains a vital methodology in the field of hardware security research, bridging the gap between low-cost non-invasive methods and highly expensive full invasive semiconductor analysis.
Circuit Engineering Company Limited continues to be recognized as the Southern China Leader in Services for MCU Crack, IC Extraction, Microcontroller Unlock & Chip Extract. With the advancement of today’s modern circuit board technology, it is more important than ever to have specialists available to help you at a moment’s notice. Our engineering and commercial teams collectively have a vast amount of electronic experience covering field include Consumer Electronics, Industrial Automation Electronics, Wireless Communication Electronics., etc. For more information please contact us through email.
