Microcontroller Units (MCUs) store firmware and critical data in their Flash and EEPROM memories. Reading these binary files is essential for reverse engineering, firmware analysis, and recovering lost data. This article explains the process of extracting binary files from an MCU’s memory while ensuring data integrity and security.
펌웨어 분석은 엔지니어가 디버깅 또는 보안 감사를 위해 독점 펌웨어를 검사하는 데 도움이 될 수 있습니다. 보호 마이크로프로세서에서 임베디드 펌웨어를 복구 및 백업하여 손실되거나 손상된 펌웨어를 복구할 수 있습니다. 잠긴 마이크로컨트롤러를 리버스 엔지니어링하여 사용자 정의 또는 보안 연구를 위한 장치 기능을 이해할 수 있습니다.
Why Read MCU Binary Files?
-
Firmware Analysis – Examine proprietary firmware for debugging or security audits.
-
Recovery & Backup – Retrieve lost or corrupted firmware for restoration.
-
Reverse Engineering – Understand device functionality for customization or security research.
Methods to Extract Binary Files
1. Using a Programmer/Debugger
Most MCUs support in-system programming (ISP) or Joint Test Action Group (JTAG) interfaces. Tools like:
-
ST-Link (for STM32)
-
AVRDUDE (for AVR MCUs)
-
J-Link (ARM-based MCUs)
Steps:
-
Connect the programmer to the MCU.
-
Use software (e.g., OpenOCD, Flashrom) to dump Flash/EEPROM.
-
Save the output as a
.binor.hexfile.

फर्मवेयर विश्लेषण, डिबगिंग या सुरक्षा ऑडिट के लिए मालिकाना फर्मवेयर की जाँच करने में इंजीनियरों की मदद कर सकता है। पुनर्स्थापना के लिए खोए या दूषित फर्मवेयर को पुनर्प्राप्त करने के लिए सुरक्षात्मक माइक्रोप्रोसेसर से एम्बेडेड फर्मवेयर की पुनर्प्राप्ति और बैकअप। अनुकूलन या सुरक्षा अनुसंधान के लिए डिवाइस की कार्यक्षमता को समझने के लिए लॉक किए गए माइक्रोकंट्रोलर की रिवर्स इंजीनियरिंग।
2. Using a Bootloader
Some MCUs have a built-in bootloader for firmware updates. Serial (UART), USB, or CAN interfaces can be used to extract memory contents.
3. Direct Memory Access (DMA) Attacks
In some cases, attackers exploit vulnerabilities to dump memory. Ethical hackers use this for security testing.
Challenges & Protection Measures
-
Read Protection Bits – Many MCUs have security fuses to prevent unauthorized reading.
-
Encrypted Firmware – Some devices encrypt Flash memory, requiring decryption keys.
-
Physical Extraction – If software methods fail, chip-off attacks (desoldering and reading via SPI/I2C) may be necessary.
Best Practices
✔ Backup Original Firmware – Always keep a copy before modification.
✔ Use Legitimate Tools – Avoid unreliable software that may corrupt data.
✔ Respect Legal Boundaries – Only read firmware you own or have permission to access.
Phân tích firmware có thể giúp kỹ sư kiểm tra firmware độc quyền để gỡ lỗi hoặc kiểm tra bảo mật.
Phục hồi & Sao lưu firmware nhúng từ Bộ vi xử lý bảo vệ để Truy xuất firmware bị mất hoặc bị hỏng để khôi phục.
Kỹ thuật đảo ngược bộ vi điều khiển bị khóa để Hiểu chức năng thiết bị nhằm tùy chỉnh hoặc nghiên cứu bảo mật.
Conclusion
Reading an MCU’s binary file from Flash and EEPROM requires the right tools and techniques. Whether for recovery, analysis, or security research, understanding memory extraction is crucial for embedded system professionals. Always follow ethical guidelines and manufacturer specifications to avoid damaging the device.
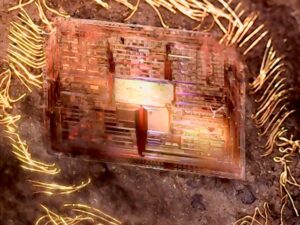
Read MCU Binary File has a lot of different ways and fault injection read has long been recognized as one of the most effective and efficient methods. It is a new method to read MCU. Through the light energy transmitting onto the target transistor to affect their status, after that a transient mistake can be generated consequently when read MCU. It is a very practical MCU read method since it requires no expensive laser generator and emitter. All we need to have to use for MCU reading is a second hand flash light and laser indicator purchased from photographer shop. In order to better illustrate the read MCU capability by fault injection read, we have been researched the random SRAM bits beneath or reset locations of microscopy.

การวิเคราะห์เฟิร์มแวร์สามารถช่วยวิศวกรตรวจสอบเฟิร์มแวร์ที่เป็นกรรมสิทธิ์สำหรับการดีบักหรือการตรวจสอบความปลอดภัย การกู้คืนและสำรองข้อมูลเฟิร์มแวร์แบบฝังตัวจากไมโครโปรเซสเซอร์ป้องกันเพื่อดึงเฟิร์มแวร์ที่สูญหายหรือเสียหายกลับมาใช้ใหม่ วิศวกรรมย้อนกลับไมโครคอนโทรลเลอร์ที่ล็อกไว้เพื่อทำความเข้าใจฟังก์ชันการทำงานของอุปกรณ์สำหรับการปรับแต่งหรือการวิจัยด้านความปลอดภัย
If there is no anti-measures, even the optical probing can have errors in the secret key calculation or protocol, and pause the control procedure of processor when read MCU. Fault injection read has not only already extended the current noise and fault analysis technologies which are also belong to the MCU reading methods, but also brought great troubles to the industry, similar to the microprobe MCU read in the middle of 1990 as well as the power analysis read in the late 1990.
