Extract IC through its backside and acquire its firmware is quite normal in the IC extracting industry. Most modern chips have secured front-side protections, including encrypted memory, locked debug interfaces, and tamper-resistant coatings. By targeting the backside of the IC, attackers bypass these defenses, gaining direct access to the binary data stored in EEPROM or flash memory. This method is especially useful when traditional decryption or decoding fails.
Volcar el contenido de la memoria: se utilizan herramientas avanzadas como el sondeo asistido por láser o el haz de iones enfocado (FIB) para copiar o volcar los datos hexadecimales.
Ingeniería inversa: el archivo extraído se analiza para replicar el firmware o restaurar el programa original.
Clonar o duplicar: una vez recuperados los datos por completo, los atacantes pueden duplicar el chip o modificar su funcionalidad.
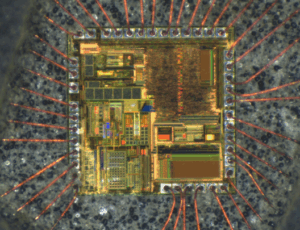
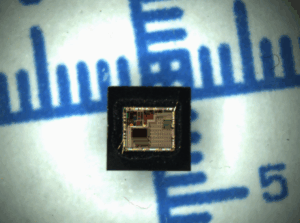
Carry out the same operation through the bottom side of IC can achieve the extracting result too. But the IC extracting operation could be more difficult than from the top side. From one aspect, it is not easy to find the security fuse location from the IC backside. From the other side, IC extracter can use brutal mechanical force to de-capsulate the IC which can avoid the usage of strong acid solution. Anyway, IC extracter can take the top side optical photography as reference to locate its security fuse, or use infrared lens to locate it.
Although there is not enough 1 to 1.1 microns infrared light can be obtained from halogen light bulbs which will be used to ionized effective zone of transistor from the backside of IC when IC extract, but tremendous ions pair of holes from the silicon button will fall onto the effective area before mutual combination.
-
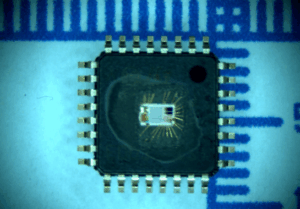
Decapsulate the Chip – The IC is carefully opened using chemical or mechanical methods to expose the silicon die.
-
Dump Memory Contents – Advanced tools like laser-assisted probing or Focused Ion Beam (FIB) are used to copy or dump the heximal data.
-
Reverse Engineering – The extracted file or archive is analyzed to replicate the firmware or restore the original program.
-
Clone or Duplicate – Once the data is fully recovered, attackers can duplicate the chip or modify its functionality.
Bellek İçeriğini Boşaltma – Lazer destekli sondaj veya Odaklanmış İyon Işını (FIB) gibi gelişmiş araçlar, altıgen verileri kopyalamak veya boşaltmak için kullanılır.
Tersine Mühendislik – Çıkarılan dosya veya arşiv, aygıt yazılımını çoğaltmak veya orijinal programı geri yüklemek için analiz edilir.
Klonlama veya Kopyalama – Veriler tamamen kurtarıldığında, saldırganlar çipi kopyalayabilir veya işlevselliğini değiştirebilir.
Unfortunately, this kind of IC extract method can’t deal with the modern low featured size IC. Top metal layer can prevent the light from reaching the effective area, complanation can decrease the transparency of oxidation layer when extract IC, and strength the light separation. High doping potency can decrease the light penetration from backside of IC when extract it. Smaller transistor requires to use stronger radiation to extract IC.
This technique is used for recovering lost firmware, hacking proprietary systems, or breaking DRM protections. However, it also poses risks—malicious actors can attack secure systems, steal intellectual property, or clone authentication chips.
Ultraviolet EEPROM memorizer unit is not so sensitive to the light IC extract method, as a result of that, IC extracter need to more powerful current to stimulate it. However, the fact is flash lamp or general light bulb can be used to extract the IC security fuse, and still need to design the security method to keep away from the IC extract carefully.
For instance, security fuse shouldn’t be placed in the area where is far away from the main memorizer which can cause the extract IC become easier. At the same time, light and radiation sensor can use to inspect the ion radiation, reset the IC before the sensitive and important information being released.
Дамп содержимого памяти — для копирования или дампа шестнадцатеричных данных используются передовые инструменты, такие как лазерное зондирование или сфокусированный ионный пучок (FIB).
Обратное проектирование — извлеченный файл или архив анализируется для копирования прошивки или восстановления исходной программы.
Клонирование или дублирование — после полного восстановления данных злоумышленники могут дублировать чип или изменять его функциональность.
Extract IC Through Backside is a powerful method in reverse engineering, allowing experts to bypass front-side protections and access critical memory data. While useful for recovery and research, it highlights the need for stronger hardware security measures. By understanding these techniques, engineers can better protect their designs from unauthorized decryption and replication.
