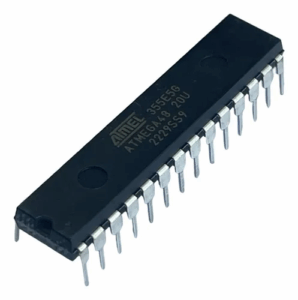
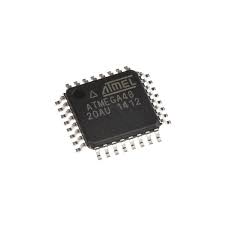
The demand to extract IC ATMEGA48 heximal arises in many real-world applications where critical firmware stored inside a secured microcontroller must be recovered, cloned, or restored. The ATmega48, part of Microchip’s AVR family (originally by Atmel), is an 8-bit RISC-based MCU featuring 4KB of in-system programmable flash, 512 bytes of EEPROM, and 512 bytes of SRAM. With powerful peripherals, low power consumption, and robust performance, it has been widely deployed in consumer electronics, industrial automation, medical devices, and automotive control systems.

In many products, the ATmega48 hosts the proprietary program that determines the unique behavior of the device. This binary is often locked behind strong security fuses, ensuring that the memory cannot be accessed through standard programming interfaces. When companies need to dump the original heximal or binary file — perhaps to restore lost source code, replicate discontinued designs, or duplicate legacy hardware — they face the serious challenge of overcoming protected and encrypted firmware barriers.
The process of extracting the internal data from such a chip requires highly specialized reverse engineering techniques. Direct attempts to copy or clone via ISP/JTAG interfaces will usually fail once the security bits are set. As a result, advanced methods must be used, including:
-
Decapsulation: Chemically or mechanically removing the chip’s packaging to expose the silicon die, allowing for laser or microprobe attack on the memory cells.
-
Fault injection: Using voltage or clock glitches to temporarily bypass the locked state and enable partial readout of flash or EEPROM.
-
Side-channel analysis: Monitoring subtle variations in power or electromagnetic leakage to decode the internal operations of the MCU.
-
Optical probing or microprobing: Physically interacting with the die surface to retrieve archive data bit by bit.
Each of these approaches demands precision equipment, deep technical expertise, and extensive experimentation. The ATmega48 is engineered with hardware countermeasures to make breaking, cracking, or hacking it far from trivial. Even when one gains access, the firmware may be encrypted, requiring further decryption before it can be reconstructed into a usable heximal file.
Industrially, the ATmega48 is commonly deployed in security systems, motor controllers, sensor nodes, and even automotive ECUs. Its reliable performance in protected environments makes it attractive for mission-critical designs, but this also means that recovering the internal archive demands extraordinary effort. For companies managing product life cycles or repairing legacy systems, the ability to extract IC ATMEGA48 heximal can be the only way to keep production lines operational or maintain compatibility with older hardware.
Extract IC ATMEGA48 Heximal include the content from its flash memory and data from eeprom memory, the firmware can be programmed into blank MCU ATmega48 which will provide the same functions as original Microcontroller ATmega48 for IC clone;
Features
- High Performance, Low Power AVR® 8-Bit Microcontroller
- Advanced RISC Architecture
– 131 Powerful Instructions – Most Single Clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
– Up to 20 MIPS Throughput at 20 MHz
– On-chip 2-cycle Multiplier
Non-volatile Program and Data Memories if copy microcontroller program
– 4/8/16K Bytes of In-System Self-Programmable Flash (ATmega48/88/168)
Endurance: 10,000 Write/Erase Cycles
– Optional Boot Code Section with Independent Lock Bits
In-System Programming by On-chip Boot Program
True Read-While-Write Operation
– 256/512/512 Bytes EEPROM (ATmega48)
Endurance: 100,000 Write/Erase Cycles
– 512/1K/1K Byte Internal SRAM (ATmega48/88/168)
– Programming Lock for Software Security
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescaler and Compare Mode after read microcontroller firmware
– One 16-bit Timer/Counter with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Six PWM Channels
– 8-channel 10-bit ADC in TQFP and QFN/MLF package
– 6-channel 10-bit ADC in PDIP Package
– Programmable Serial USART
– Master/Slave SPI Serial Interface

– Byte-oriented 2-wire Serial Interface (Philips I2C compatible)
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
– Interrupt and Wake-up on Pin Change
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection after remove chip extraction protection
– Internal Calibrated Oscillator
– External and Internal Interrupt Sources
– Five Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, and Standby I/O and Packages
– 23 Programmable I/O Lines
– 28-pin PDIP, 32-lead TQFP, 28-pad QFN/MLF and 32-pad QFN/MLF
Operating Voltage:
– 1.8 – 5.5V for ATmega48V/88V/168V
– 2.7 – 5.5V for ATmega48/88/168
Temperature Range:
– -40°C to 85°C
Speed Grade:
– ATmega48V/88V/168V: 0 – 4 MHz @ 1.8 – 5.5V, 0 – 10 MHz @ 2.7 – 5.5V
– ATmega48/88/168: 0 – 10 MHz @ 2.7 – 5.5V, 0 – 20 MHz @ 4.5 – 5.5V
Low Power Consumption
– Active Mode:
250 µA at 1 MHz, 1.8V
15 µA at 32 kHz, 1.8V (including Oscillator)
– Power-down Mode:
0.1µA at 1.8V
In summary, extracting the firmware or binary dump from a secured ATmega48 microcontroller is a formidable task involving a combination of reverse engineering science and practical chip attack techniques. The balance between protection and accessibility defines the uniqueness of this MCU: it is simple enough for widespread use across industries, yet locked tightly enough to make duplication or recovery an exercise in advanced hardware security expertise.
