The process of Extract IC code refers to the advanced technological approach of retrieving a binary file, firmware, or source code from a secured or encrypted chip such as a microcontroller (MCU) or microprocessor. This technique, which lies at the heart of reverse engineering, is widely applied in various fields—from industrial hardware maintenance to academic research and legacy system recovery.
Fiziksel erişim için silikon kalıbı açığa çıkarmak üzere çip paketini kapsülden çıkarın.
Glitching, lazer hata enjeksiyonu veya yan kanal analizi gibi teknikler kullanarak dahili güvenliğe saldırın veya kırın.
Kilitli aygıt yazılımı bölgelerini kod çözün, şifresini çözün veya hackleyin.
Kullanılabilir bir ikili veya altıgen dosya elde etmek için EEPROM, flash veya gömülü belleğin içeriklerini boşaltın veya kopyalayın.
Aygıta başarıyla erişildikten sonra, çıkarılan veriler analiz, yedekleme veya cihaz klonlama için geri yüklenebilir, çoğaltılabilir veya kopyalanabilir.
Secured chips often protect their internal memory through sophisticated locking mechanisms. These protections may include encryption, code readout protection, and memory region locking. Extracting firmware or data from such a chip requires in-depth knowledge and highly specialized tools.
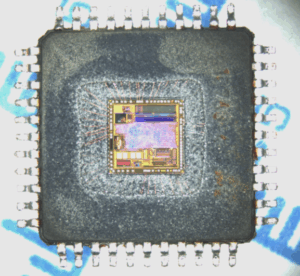
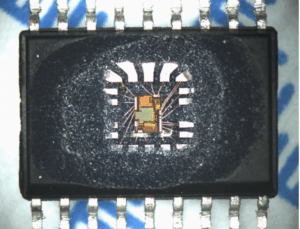
Extract IC code from its embedded and encrypted memorizers like FLASH & EEPROM can have a great variety of methods, which include the non-invasive IC extraction, semi-invasive IC extraction which has both the cost advantage and shorter time cycle, and finally the most expensive and which has also been specified as the last method to overcome those difficult IC extraction is invasive one.
The process typically starts by identifying the target chip’s architecture and protection mechanisms. To extract the data, engineers may use methods like:
-
Decapsulate the chip package to expose the silicon die for physical access.
-
Attack or crack the internal security using techniques such as glitching, laser fault injection, or side-channel analysis.
-
Dump or copy the contents of EEPROM, flash, or embedded memory to obtain a usable binary or heximal file.
After successfully accessing the firmware, the extracted data may be restored, replicated, or duplicated for analysis, backup, or device cloning.
Декапсуляция корпуса чипа для физического доступа к кремниевому кристаллу.
Атака или взлом внутренней безопасности с использованием таких методов, как сбой, лазерная инъекция неисправностей или анализ побочных каналов.
Декодирование, расшифровка или взлом заблокированных областей прошивки.
Сброс или копирование содержимого EEPROM, флэш-памяти или встроенной памяти для получения пригодного к использованию двоичного или шестнадцатеричного файла.
После успешного доступа к прошивке извлеченные данные могут быть восстановлены, реплицированы или дублированы для анализа, резервного копирования или клонирования устройства.
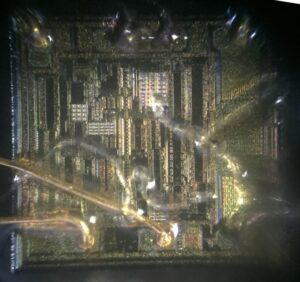
As one of the non-invasive IC extraction method, modeling attacks has played the role for a while since the day it has been invented and developed. So in order to research the effective measurement, it is critical to understand the code extraction details. In the optical light injection and laser scanning attack methods, IC cracker need to fully understand the operation process and principle in the semiconductor IC.
Breaking into protected or locked chips is not without significant challenges. Modern ICs implement robust countermeasures designed specifically to prevent code readout. Some common difficulties include:
-
Tamper-detection circuits that destroy memory contents upon unauthorized access attempts.
-
Multi-layered protection mechanisms that require simultaneous bypass of both hardware and software defenses.
Moreover, improper handling during decapsulation can permanently damage the chip, resulting in complete data loss. Even if the program is successfully extracted, reconstructing the original firmware or source code from a binary dump can be a complex and time-consuming process, requiring in-depth knowledge of embedded systems and disassembly tools.
Dekapsulacja obudowy układu, aby odsłonić krzemowy układ scalony w celu uzyskania dostępu fizycznego.
Atak lub złamanie wewnętrznych zabezpieczeń za pomocą technik, takich jak glitching, wstrzykiwanie błędów laserowych lub analiza kanału bocznego.
Dekodowanie, odszyfrowywanie lub hakowanie zablokowanych regionów oprogramowania układowego.
Zrzucanie lub kopiowanie zawartości pamięci EEPROM, flash lub pamięci osadzonej w celu uzyskania użytecznego pliku binarnego lub heksametalogowego.
Po pomyślnym uzyskaniu dostępu do oprogramowania układowego wyodrębnione dane mogą zostać przywrócone, zreplikowane lub zduplikowane w celu analizy, utworzenia kopii zapasowej lub klonowania urządzenia.
And simulate this kind of IC code extraction will have a lot of restriction. Each step need to tackle with multiple aspects in the complicate system. And it could be pretty difficult to calculate a beam of laser affection on the IC extraction. But for a small part of transistors, it is possible to make the simulation. In the TCAD software, and can simulate ion radiation effects for the semiconductor IC. But this software is just too expensive and too complicate, so we should choose another one tool name DIODE-2D.
Extract IC code is a cutting-edge practice combining elements of cryptanalysis, physical hacking, and electronic forensics. Whether the goal is to recover legacy systems, restore corrupted firmware, or replicate an industrial control board, mastering this process demands technical precision and strategic thinking.
