In embedded systems development and analysis, understanding various Read MCU Methods is essential when accessing data stored inside a microcontroller (MCU). These methods are commonly used for purposes such as firmware recovery, reverse engineering, legacy system restoration, or even cloning of hardware functionality.

Microcontrollers typically store firmware, program files, and configuration data in internal flash, EEPROM, or other types of memory. When security features are not enabled, accessing this data can be as simple as using a programmer or debugger to read out the binary or heximal file through standard communication interfaces like UART, SPI, or JTAG.
However, in real-world scenarios, most MCUs are secured, protected, or even encrypted to prevent unauthorized access. In such cases, advanced Read MCU Methods must be used, including:
-
Debug Interface Exploitation: Bypassing or exploiting flaws in debug protocols to gain read access to locked memory.
-
Voltage or Clock Glitching: Introducing transient faults to bypass security logic temporarily.
-
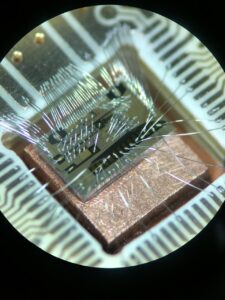
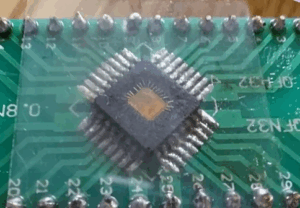
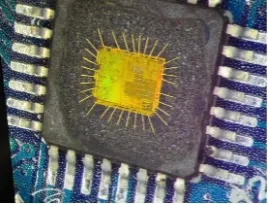
Decapsulation and Microscopy: Removing the chip’s packaging to physically analyze and identify critical memory areas or fuse bits under a microscope.
-
Laser Fault Injection: Using a focused laser beam to disrupt internal logic during boot or security check routines.
-
Side-Channel Attacks: Monitoring power usage or electromagnetic emissions to decode internal processes.
Each method has its own level of risk, complexity, and hardware requirements. In cases where firmware, source code, or data archives are no longer accessible through conventional means, these read methods provide a path to recover, replicate, or duplicate the original software logic.
In summary, Read MCU Methods encompass a range of basic to advanced techniques used to extract information from microcontrollers, whether for debugging, migration, or reverse engineering of secured chips.
Read MCU memory software can have a great variety of methods, one of them is GLITCH Read. It is a way which will swiftly change the signals input into the MCU to affect its normal operation.
Generally speaking the glitching is overlapped on the power supply or timing clock, but the glitching can also be the transient electrical field or electro-magnetic impulse. Place two minor metal needles on the several hundreds of microns away from the surface of MCU, and then add hundreds of voltage with narrow impulse with less than 1 micro-second. The safer bottom can sense the electrical field when read MCU and force the adjacent transistors voltage value change.
There is one way in recent days about advanced MCU binary extraction: use hundreds of metal coils to roll the needle tips of microprobe and constitute a minor inductor. When the current go through the coil will generate magnetic field, tips can focus the magnetic lead. Each one of the transistors can form the time extensive RC circuit with the tracks they are connect with. The maximum timing frequency of processor depends on the maximum delay on the circuit.
At the same time, each trigger in the microcontroller at89lv52 code extraction has a featured time windows among the received input voltage and output voltage caused by it. This windows used is designed and confirmed by the specific voltage and temperature. If use clock noise (which is much shorter than the normal impulse) or power supply noise (the swift wave vibration in the power supply voltage) will affect the transistors in the MCU cracking.
And will contribute directly to lead other one or several triggers into the wrong instructions, sometimes even can’t be supported by microcode. Although we can’t foresee what kind of noise will probably cause which mistake when MCU at89lv55 code extraction, but it can proceed the systematic search simply.
