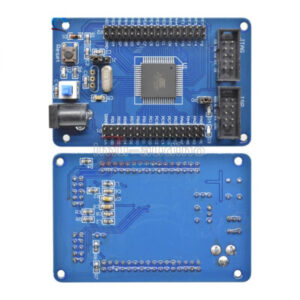
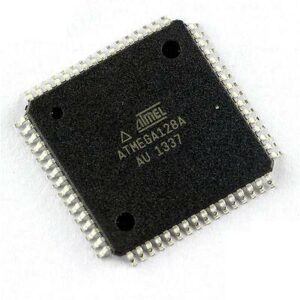
The phrase Read IC ATmega128A Firmware captures a real-world need in embedded systems: accessing a microcontroller’s stored program or binary for legitimate purposes such as recovery, maintenance, interoperability, or security research. The ATmega128A — an 8‑bit AVR microcontroller with a relatively large on‑chip flash memory — is widely used where a balance of processing capability and low cost is required. Its on‑chip resources (substantial flash for firmware, EEPROM for calibration/data, SRAM for run‑time state) and rich peripheral set (serial interfaces, timers, ADC, memory interface) make it common in industrial controllers, communication equipment, consumer appliances, and legacy hardware platforms.

Why someone would want to read IC ATmega128A firmware varies. Typical, lawful motivations include recovering a lost firmware archive when source code has been misplaced, auditing program logic for security or safety, enabling product maintenance in long‑lived systems, or creating interoperable replacement modules when a manufacturer is no longer available. In regulated industries — industrial automation, medical devices, and some automotive subsystems — being able to access the binary or heximal file can be essential to demonstrate compliance, replicate a failed board, or restore a critical service.
Read IC ATmega128A Firmware needs to break mcu atmega128a flash memory and extract embedded firmware from atmega128a microprocessor;

The Atmel QTouch Library provides a simple to use solution to realize touch sensitive interfaces on most Atmel AVR microcontrollers. The QTouch Library includes support for the QTouch and QMatrix acquisition methods.
Touch sensing can be added to any application by linking the appropriate Atmel QTouch Library for the AVR Microcontroller. This is done by using a simple set of APIs to define the touch channels and sensors to extract ic controller atmega8535 source code, and then calling the touch sensing API’s to retrieve the channel information and determine the touch sensor states.
The QTouch Library is FREE and downloadable from the Atmel website at the following location: www.atmel.com/qtouchlibrary. For implementation details and other information, refer to the Atmel QTouch Library User Guide – also available for download from the Atmel website.
This datasheet contains simple code examples that briefly show how to use various parts of the device. These code examples assume that the part specific header file is included before compilation. Be aware that not all C compiler vendors include bit definitions in the header files and interrupt handling in C is compiler dependent.
Please confirm with the C compiler documentation for more details. For I/O registers located in extended I/O map, “IN”, “OUT”, “SBIS”, “SBIC”, “CBI”, and “SBI” instructions must be replaced with instructions that allow access to extended I/O. Typically “LDS” and “STS” combined with “SBRS”, “SBRC”, “SBR”, and “CBR”.
The Atmel QTouch Library provides a simple to use solution to realize touch sensitive interfaces on most Atmel AVR microcontrollers. The QTouch Library includes support for the QTouch and QMatrix acquisition methods.
Touch sensing can be added to any application by linking the appropriate Atmel QTouch Library for the AVR Microcontroller. This is done by using a simple set of APIs to define the touch channels and sensors to extract microcontroller atmega162v flash memory code, and then calling the touch sensing API’s to retrieve the channel information and determine the touch sensor states.
The QTouch Library is FREE and downloadable from the Atmel website at the following location: www.atmel.com/qtouchlibrary. For implementation details and other information, refer to the Atmel QTouch Library User Guide – also available for download from the Atmel website.

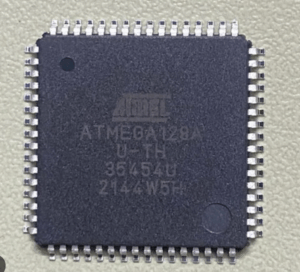
However, many deployments deliberately mark device memory as secured, locked, or protected. Vendors apply these protections to prevent unauthorized copy, clone, or duplication of proprietary code and to protect intellectual property and user safety. The presence of lock bits, encrypted firmware containers, or fused security states increases the difficulty of extracting a usable dump of the MCU’s memory or program. Attempting to bypass those protections without authorization raises serious legal and ethical concerns and may violate copyright, device licensing, and local law.
From a high level, the main challenges encountered when attempting to access protected ATmega128A firmware are non‑trivial:
-
Protection states: Logical protections can render standard read commands ineffective; this is why manufacturers use lock bits and configuration fuses to prevent casual readout of flash or EEPROM.
-
Physical constraints: The chip’s package, PCB layout, and lack of exposed debug pads often make physical access difficult without risking damage to the board or chip — which could permanently destroy the very data one seeks to recover.
-
Data interpretation: Even with a raw dump file, reconstructing meaningful source code or intent from a compiled binary is a complex reverse engineering task requiring expertise in AVR assembly, symbol reconstruction, and protocol analysis.
-
Safety and risk: In regulated products, altering or incorrectly restoring firmware can introduce hazards; preservation and integrity are paramount.
Because of these challenges and the potential for misuse, discussions about breaking protections should remain in the domain of high‑level ethics, policy, and lawful practice. When the goal is legitimate — archival, repair, or certification — the preferred routes are to seek manufacturer cooperation, obtain explicit authorization from the device owner, or engage professional services that operate within legal boundaries. Reverse engineering for security auditing or interoperability is a valid and important activity, but it must be carried out responsibly, documenting provenance of any firmware, respecting copyright and licensing, and preserving device safety.
In sum, Read IC ATmega128A Firmware is a phrase that points to a challenging, often necessary, and always sensitive activity. The ATmega128A’s capabilities and common deployments make it an important target for lawful recovery and analysis, yet its protections, physical packaging, and legal context ensure those efforts must be pursued with care, expertise, and proper authorization.