Invasive MCU extraction refers to the most extreme and technical method of retrieving firmware, binary, or source code from a secured or encrypted microcontroller (MCU). Unlike software-based attacks, which exploit weaknesses in debugging or communication protocols, invasive techniques directly target the physical silicon of a microprocessor to bypass protected memory restrictions.
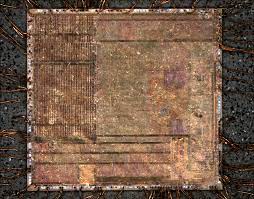
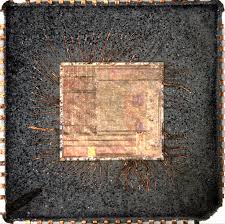
This method is reserved for high-value data recovery — such as when a program, EEPROM, or flash content is deeply locked, rendering non-invasive techniques ineffective. In such cases, engineers resort to decapsulation, where the plastic casing of the chip is chemically removed to expose the bare silicon die. Once exposed, the actual layout of the memory cells can be analyzed under a high-resolution electron microscope.
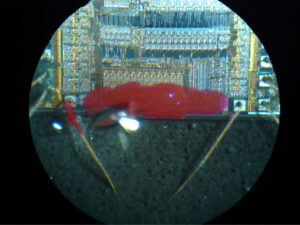
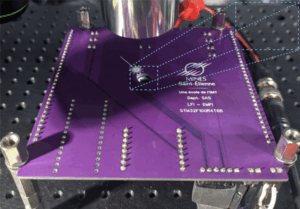
One of the most powerful tools in invasive MCU extraction is Scanning Electron Microscopy (SEM) combined with Focused Ion Beam (FIB) milling. These tools allow precise manipulation and imaging of the memory structure to locate the regions where data, firmware, or heximal codes reside. Once identified, probes or lasers can interact with these regions to extract the binary dump.
However, this level of reverse engineering is not without obstacles. Many MCUs implement hardware-level countermeasures designed to thwart invasive attacks. For example:
-
Silicon coating or mesh layers that detect intrusion or probing attempts and erase memory contents.
-
Redundant memory encoding that scrambles data storage across the die.
-
Self-destruct circuits that permanently damage the chip upon exposure.
These features make it extremely difficult to clone, duplicate, or replicate the original program file without triggering protection. Furthermore, interpreting raw memory content requires understanding undocumented logic and decrypting bitstreams that may not follow standard encoding.
Despite these barriers, invasive MCU extraction is often the only viable method to recover legacy data archives, perform restoration of bricked systems, or conduct forensic-level copying of embedded code. It’s a cornerstone in high-end firmware cracking, used in fields such as industrial espionage, device refurbishment, or IP protection auditing.
In summary, invasive MCU extraction is the apex of chip-level hacking, demanding surgical precision, deep hardware knowledge, and cutting-edge lab equipment. It’s what separates surface-level attacks from the elite processes used to break, decode, and restore highly protected embedded systems.
Invasive MCU Extraction could be viewed as the most effective and brilliant technology for the whole MCU reading industry. As we all know the Microcontroller code extraction technology can be separated into three different categories, first is un-invasive MCU cracking and reading, second is semi-invasive MCU breaking and third is invasive microcontroller unlocking.
Invasive MCU unlocking need to contact the MCU internal structure directly, if there is a security mode or watch dog, then we need to open it and then read the memorizer content in the MCU. As for the smartcard or microcontroller, we need to open its package before MCU at89ls63 eeprom extraction, use focus ion beam or laser to remove the deactivation layer and then get in touch with the internal wires embed deeply beneath it.
Invasive MCU cracking need to be equipped with excellent facilities and extractioner with great amount of experience. Meanwhile, accompany with the increase of MCU complexity and decrease of MCU size, the cost of extract microcontroller heximal become higher than before. Some operations such as decapsulation or chemical erosion can be completed by almost anyone which require only little investment and limited knowledge. Furthermore, if we read the mask rom with old version use optical method of reverse engineering the MCU with only two metal layers and one micron wire space could be much easier.
Normally, the expensive invasive MCU cracking will be used as the way to understand MCU, and then find better solutions for cheaper and faster un-invasive microcrontroller breaking.
