The concept of extract MCU power glitches represents a sophisticated method in the field of reverse engineering and embedded security research. Unlike basic software tools, power glitching involves manipulating the electrical supply to a microcontroller (MCU) at precise moments during its operation. By exploiting the chip’s vulnerabilities, engineers attempt to bypass the secured mechanisms that prevent access to its internal flash, EEPROM, or program memory.
Modern microcontrollers and microprocessors are widely deployed across industries such as automotive electronics, aerospace, industrial automation, medical devices, and consumer products. These chips store vital firmware, binary files, and data archives that dictate system functionality. For example, an automotive MCU may contain encrypted control algorithms for an engine management system, while a medical device MCU could hold proprietary source code ensuring safety compliance. Because such locked devices are crucial to long-term operation, the ability to recover or restore the embedded program can be critical when the original design files are lost or the manufacturer no longer supports the hardware.
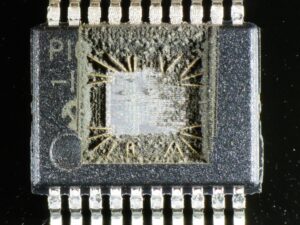
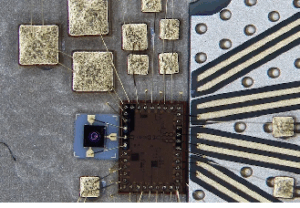
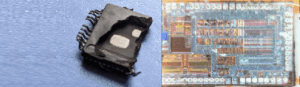
The attack method of using power glitches aims to momentarily disturb the chip’s protective features. A carefully timed glitch in the voltage supply can cause the MCU to skip security checks, allowing partial or full access to the flash memory or EEPROM dump. This process does not involve permanently damaging the chip, unlike some invasive methods such as decapsulation, but instead requires high-precision timing equipment, oscilloscopes, programmable power supplies, and often a deep understanding of the target device’s internal operation.

Once the glitch succeeds, researchers may gain the ability to copy, clone, or duplicate the original firmware into a binary or heximal archive for analysis. The extracted file can then be examined, decoded, and potentially decrypted to reveal the underlying source code or logic. This recovered data is invaluable for system maintenance, creating compatible replacements, or performing deeper reverse engineering tasks.
The vibration in the power supply voltage will cause the shifting of transistor electrical level value which can be used for Extract MCU Power Glitches. The result is the triggers in it can sample their input in different times when we try to crack MCU, or extract the wrong security fuse state.
Normally the instantaneous power supply voltage increase or decrease will generate noise, so generally within 10 cycles of MCU extract, power supply noise will be applied on the program interfaces of MCU which can affect the processor operation or the hardware security circuit. Weak point can be more difficult to use than time noise. Since for time zone parameters, vibration, up/down time length are all variables.
A example is extract MCU MC68C05B6, if the power supply voltage decrease to 50-70% when operate the instruction. The processor can extract the value FFh from the EEPROM instead of the real value. This can refers to the security fuse unencrypted state.
The trick is calculate the operation time carefully to decrease the voltage, otherwise the processor will go into the pause situations or reset states. This kind of extract mcu embedded firmware task is not difficult, target order will be operated after reset within the first 100 cycles. MCU extracter can use vector generator to build a noise source of his own.
However, the process of extract MCU power glitches is fraught with difficulties. Many secured MCUs have countermeasures such as voltage sensors, watchdog timers, or redundant protection states that make glitching inconsistent. Timing windows are often measured in nanoseconds, requiring hundreds or thousands of attempts before success. Even when successful, the output may only yield fragmented program sections, requiring additional hack strategies to reconstruct the complete firmware archive. Moreover, if the chip incorporates encrypted storage, additional cryptanalysis must be performed after the initial glitch-based bypass.
What makes this technique especially complex is the combination of electronic engineering, embedded systems knowledge, and practical experimentation required. Unlike brute-force attacks or software-only exploits, glitch-based extraction demands patience and advanced laboratory setups.
In summary, to extract MCU power glitches is to apply a refined and precise attack methodology for retrieving secured firmware from a locked microcontroller. By temporarily disturbing the hardware at just the right instant, it becomes possible to recover, replicate, and restore valuable embedded data archives that would otherwise remain inaccessible. This approach highlights the balance between robust MCU security design and the persistence of engineers determined to unlock the secrets hidden within the memory of protected chips.
