The phrase extract MCU embedded firmware refers to the highly specialized process of retrieving a binary file or heximal dump from a microcontroller (MCU) or microprocessor that has been deliberately protected against unauthorized access. Unlike simple memory readouts from unprotected devices, modern MCUs are often equipped with secured, encrypted, or locked mechanisms that prevent direct access to internal flash, EEPROM, or program memory.
Odzyskiwaniu starszych systemów, w których oryginalny kod źródłowy lub archiwum został utracony. Klonowaniu lub replikowaniu produktów do celów testowych i rozwojowych. Przywracaniu uszkodzonych systemów poprzez przeprogramowanie nowych mikrokontrolerów (MCU) z wykorzystaniem oryginalnego zrzutu plików. Przeprowadzaniu inżynierii wstecznej w celu analizy funkcjonalności lub identyfikacji luk w zabezpieczeniach. Jednak osiągnięcie tego celu rzadko jest proste. Mikrokontrolery (MCU) są celowo projektowane z funkcjami zabezpieczającymi, takimi jak bity blokady odczytu, zaszyfrowane bloki pamięci, a nawet sprzętowe czujniki antysabotażowe. Tworzą one istotne bariery dla każdego, kto próbuje włamać się, zhakować lub zaatakować urządzenie.
An MCU is the core element of countless electronic products. It integrates CPU, memory, and peripherals into a single chip, offering compact, efficient, and reliable control. These devices are widely deployed in industries ranging from automotive (engine control units, airbags, anti-lock braking), consumer electronics (smart appliances, wearable devices), and industrial automation (robotics, process control) to medical electronics (diagnostic equipment, infusion pumps, monitoring devices). The firmware embedded in these chips contains the source code, data, and program files essential for product functionality.
When a system requires maintenance, recovery, or replication, engineers may need to extract MCU embedded firmware. This operation can serve various purposes:
-
Recovering legacy systems where the original source code or archive has been lost.
-
Cloning or replicating products for testing and development.
-
Restoring damaged systems by reprogramming new MCUs with the original file dump.
-
Conducting reverse engineering to analyze functionality or identify vulnerabilities.
Yet, achieving this is rarely straightforward. MCUs are deliberately designed with protection features such as readout lock bits, encrypted memory blocks, and even hardware anti-tamper sensors. These create substantial barriers for anyone attempting to break, hack, or attack the device.

Extract MCU embedded firmware need to use a series of different processes which can cause the attention from security fuse. Before The security fuse of memorizer be removed completely, there is some security flaws are still exist. Even after the elimination of security fuse, there is still no effective data can be read directly. But hereby the power glitch measure can still play its role.
For example, if the security fuse expose in the ultra-violet is over seven minutes, VDD under 2.2v can read the content from memorizer of extract mcu at89c52 heximal unspoiled. But the security fuse can be effective even after the voltage over 4.8v.
When MCU extractor can attain the precise moment of switch the data from memorizer to the migration storage and check the status of security fuse. It can probably through low down the power supply voltage to 2V and lock the memorizer and increase the voltage to 5V to get the content from extracted microcontroller at89c55 code and deactivate the security fuse.
Опоравак застарелих система где је оригинални изворни код или архива изгубљен.
Клонирање или репликација производа за тестирање и развој.
Враћање оштећених система репрограмирањем нових микроконтролера са оригиналним дампом датотека.
Спровођење обрнутог инжењеринга ради анализе функционалности или идентификације рањивости. Међутим, постизање овога ретко је једноставно. MCU-ови су намерно дизајнирани са заштитним функцијама као што су битови за закључавање читања, шифровани блокови меморије, па чак и хардверски сензори против неовлашћеног мењања. Ово ствара значајне баријере за свакога ко покуша да провали, хакује или нападне уређај.
Another trick is restore the content inside the memorizer of MCU, even if there is no overlap between security fuse elimination and unspoiled memorizer. For instance, we found the new samples of same MCU can start to disturb the content inside the memorizer before the elimination of security fuse in which the power glitch will be used to recover the content inside the MCU after extraction.
Commonly explored approaches include:
-
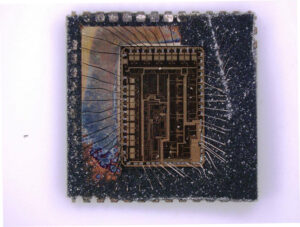
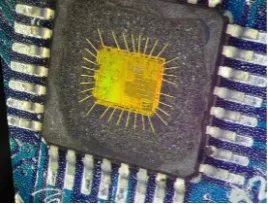
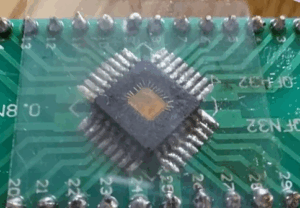
Decapsulation – Removing the MCU’s encapsulation to expose the silicon die. Once the die is visible, advanced optical or electron microscopy methods may be used to locate memory cells and extract data directly.
-
Fault Injection – Deliberately introducing glitches in voltage or clock signals to force the MCU into bypassing its secured state, sometimes allowing partial dump access to the internal firmware.
-
Side-Channel Attacks – Monitoring power consumption, electromagnetic radiation, or timing variations to indirectly decode secret operations or decryption keys used by the chip.
-
Debug or Bootloader Exploitation – In cases where the device’s debug interface has not been fully disabled, it may be possible to copy or duplicate segments of program memory.
The greatest difficulty lies in the unpredictable nature of these protected systems. Each MCU family implements different security architectures, and the cost and time required to decrypt or restore the binary archive can be extremely high. Moreover, performing such invasive chip-level hacking demands sophisticated laboratories, precision equipment, and years of reverse engineering expertise.
Only through the tunning and debugging threshold value in the transistors to extract chip firmware. Control the programming time in the memorizer carefully can inject certain amount of ions into the floating gate of MCU. Generally speaking, EPROM memorizer’s programming can be operated by external signals and all the sequence are all controlled by programming unit. Which makes the MCU cracker can have chance to inject the ions into the floating gate to change the threshold value and ensure the data can be extracted and read when the security fuse is secure and active.
Obnova starších systémů, kde byl ztracen původní zdrojový kód nebo archiv.
Klonování nebo replikace produktů pro testování a vývoj.
Obnova poškozených systémů přeprogramováním nových mikrokontrolérů s původním výpisem souborů.
Provádění reverzního inženýrství za účelem analýzy funkčnosti nebo identifikace zranitelností. Dosažení tohoto cíle však zřídka bývá přímočaré. Mikrokontroléry jsou záměrně navrženy s ochrannými funkcemi, jako jsou bity pro uzamčení čtení, šifrované paměťové bloky a dokonce i hardwarové senzory proti neoprávněné manipulaci. Ty vytvářejí značné bariéry pro kohokoli, kdo se pokusí zařízení prolomit, hacknout nebo napadnout.
In essence, to extract MCU embedded firmware is not a routine procedure but rather a meticulous engineering challenge. It blends attack strategies, physical decapsulation, and algorithmic decode methods to overcome locked hardware defenses. For industries that rely on critical embedded systems, the ability to recover, replicate, or duplicate firmware is invaluable, ensuring long-term system continuity and technological resilience.
