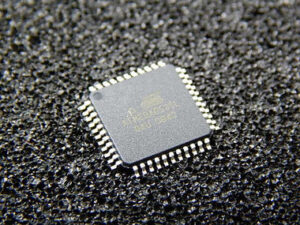
The task to extract MCU ATMEGA8535L code is one of the most intriguing and technically demanding challenges in embedded system security. The ATMEGA8535L, developed by Atmel (now Microchip), is an AVR 8-bit microcontroller that integrates 8KB of in-system programmable flash, 512B of EEPROM, and 512B of internal SRAM. With versatile peripherals such as USART, SPI, ADC, timers, and I/O capabilities, this chip has been widely deployed in industrial automation, medical instruments, automotive electronics, consumer devices, and even aerospace prototyping systems. Its low power consumption and robust performance make it a favored choice for embedded designers across different industries.

When engineers attempt to recover or restore the firmware, binary, or source code stored in the ATMEGA8535L, they encounter serious hurdles. This MCU is equipped with lock bits and fuse settings that enforce a secured and protected environment. Once enabled, these mechanisms prevent ordinary programmers from accessing the program memory, EEPROM, or any part of the firmware archive. The design ensures intellectual property protection, but it also poses a barrier for engineers who may legitimately need to copy, replicate, or duplicate the firmware for maintenance, migration, or legacy system recovery.
Extract MCU ATMEGA8535L Code from its memory include flash program and eeprom data by unlocking microcontroller ATmega8535L and disable the security fuse bit embedded in the tamper resistance system;
The ATmega8535 provides all the features of the AT90S8535. In addition, several new features are added. The ATmega8535 is backward compatible with AT90S8535 in most cases. However, some incompatibilities between the two microcontrollers exist.

To solve this problem, an AT90S8535 compatibility mode can be selected by programming the S8535C fuse. ATmega8535 is pin compatible with AT90S8535, and can replace the AT90S8535 on current Printed Circuit Boards. However, the location of fuse bits and the electrical characteristics differs between the two devices if reading MCU firmware.
Port A serves as the analog inputs to the A/D Converter. Port A also serves as an 8-bit bi-directional I/O port, if the A/D Converter is not used. Port pins can provide internal pull-up resistors (selected for each bit). The Port A output buffers have symmetrical drive characteristics with both high sink and source capability.
When pins PA0 to PA7 are used as inputs and are externally pulled low, they will source current if the internal pull-up resistors are activated. The Port A pins are tri-stated when a reset condition becomes active, even if the clock is not running. Port B is an 8-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port B output buffers have symmetrical drive characteristics with both high sink and source capability after Extract ic attiny15 software.
To bypass these protections and dump the data from the ATMEGA8535L, advanced reverse engineering techniques must be employed. Some of the strategies include:
-
Decapsulation and microprobing: Removing the packaging of the chip to directly access the silicon die, followed by probing data buses under a microscope.
-
Fault injection attacks: Using voltage, power, or clock glitches to disrupt the security state, temporarily disabling lock bits to allow a partial code dump.
-
Side-channel analysis: Monitoring power consumption, electromagnetic emissions, or timing variations to decode internal operations and indirectly extract heximal sequences of firmware.
-
Optical and laser techniques: Focusing light or laser beams on specific regions of the die to alter memory cell behavior, enabling hidden file or program access.
The main difficulty in breaking the ATMEGA8535L lies in its robust encrypted and locked fuse architecture. Each failed attempt to crack or hack into the memory risks permanently damaging the MCU, wiping the binary, or corrupting the archive beyond recovery. In addition, the integration of flash and EEPROM in a single package means that the extraction process must be carefully controlled to avoid erasing both types of data simultaneously.
As inputs, Port B pins that are externally pulled low will source current if the pull-up resistors are activated. The Port B pins are tri-stated when a reset condition becomes active, even if the clock is not running. Port C is an 8-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port C output buffers have symmetrical drive characteristics with both high sink and source capability.
As inputs, Port C pins that are externally pulled low will source current if the pull-up resistors are activated. The Port C pins are tri-stated when a reset condition becomes active, even if the clock is not running. Port D is an 8-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port D output buffers have symmetrical drive characteristics with both high sink and source capability when Extract ic attint26 binary.
As inputs, Port D pins that are externally pulled low will source current if the pull-up resistors are activated. The Port D pins are tri-stated when a reset condition becomes active, even if the clock is not running.
Nevertheless, successfully managing to extract MCU ATMEGA8535L code allows engineers to restore old projects, replicate discontinued boards, or clone existing systems for replacement in critical industrial applications. The extracted firmware can then be analyzed, modified, or ported into new hardware, ensuring business continuity even when the original design files are lost.

In conclusion, the mission to extract MCU ATMEGA8535L code is far from trivial. It requires a combination of decapsulation, attack strategies, and deep reverse engineering expertise to decrypt and recover the locked data. This process highlights the delicate balance between protecting intellectual property and ensuring long-term system reliability in industries that rely on legacy microcontroller solutions.
