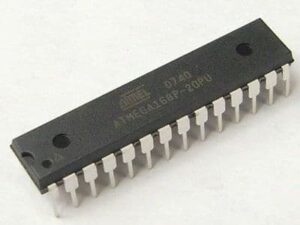
Extract MCU ATmega168P Software describes a focused, legitimate capability: retrieving a compiled binary or firmware archive from a secured, protected, or locked microcontroller so that organizations can maintain, repair, or audit their products. The ATmega168P, a well-known AVR family MCU supported by Microchip, offers a compact and efficient platform: on-chip flash for program storage, EEPROM for calibration and persistent data, SRAM for runtime state, and a flexible mix of timers, ADC, SPI, I²C and UART peripherals. These features make the ATmega168P a popular choice across consumer electronics, hobbyist boards, sensor nodes, low-end industrial controllers, and small medical or instrumentation devices.
In commercial practice, the need to extract MCU ATmega168P software often arises for entirely legitimate reasons. Clients may have lost original source code, need to recover a corrupted program after an update failure, require archival of a binary for long-term product support, or must demonstrate compliance by auditing embedded firmware. In retrofit or end-of-life scenarios, being able to obtain a usable dump of the device’s flash allows engineers to restore, replicate, or duplicate essential behavior when the original vendor no longer supports the product.
Extract MCU ATmega168P Software from cracking mcu atmega168p flash memory and replicate the avr atmel processor atmega168p memory content in the format of heximal;
The interrupt execution response for all the enabled AVR interrupts is four clock cycles minimum. After four clock cycles the program vector address for the actual interrupt handling routine is executed. During this four clock cycle period, the Program Counter is pushed onto the Stack.
The vector is normally a jump to the interrupt routine, and this jump takes three clock cycles. If an interrupt occurs during execution of a multi-cycle instruction, this instruction is completed before the interrupt is served. If an interrupt occurs when the MCU is in sleep mode, the interrupt execution response time is increased by four clock cycles. This increase comes in addition to the start-up time from the selected sleep mode.
Conversations about this work commonly use verbs such as crack / break /attack /decode /decapsulate /hack /decrypt /clone /copy /recover /replicate /duplicate /restore /reverse engineering, and nouns like firmware / source code / binary / heximal / EEPROM / flash / program / memory / file / data / archive / microcontroller / microprocessor / chip / MCU / dump. Adjectives such as secured / protected /encrypted /locked highlight the context: manufacturers often enable protections to prevent unauthorized copy or intellectual-property theft, which raises both technical and legal boundaries around any extraction effort.
The practical difficulties of working with a protected ATmega168P are significant and multi-faceted. Logical protections such as lock bits and fuse settings are intended to block standard readout; physical realities — tiny packages, dense multilayer PCBs, and absent debug headers — make non-destructive access challenging. A raw binary file by itself is also of limited immediate use: compiled machine code lacks original symbols and comments, so meaningful analysis requires expert reverse engineering to interpret control flow, reconstruct algorithmic intent, and safely re-implement features without introducing regressions.
A return from an interrupt handling routine takes four clock cycles. During these four clock cycles, the Program Counter (two bytes) is popped back from the Stack, the Stack Pointer is incremented by two, and the I-bit in SREG is set.
This section describes the different memories in the ATmega168. The AVR architecture has two main memory spaces, the Data Memory and the Program Memory space. In addition, the ATmega168 features an EEPROM Memory for data storage. All three memory spaces are linear and regular.
The ATmega168 contains 4/8/16K bytes On-chip In-System Reprogrammable Flash memory for program storage. Since all AVR instructions are 16 or 32 bits wide, the Flash is organized as 2/4/8K x 16. For software security, the Flash Program memory space is divided into two sections, Boot Loader Section and Application Program Section in ATmega88 and ATmega168.
ATmega48 does not have separate Boot Loader and Application Program sections, and the SPM instruction can be executed from the entire Flash. See SELFPRGEN description in section ”SPMCSR – Store Program Memory Control and Status Register” on page 267 and page 283for more details.
The Flash memory has an endurance of at least 10,000 write/erase cycles. The ATmega48/88/168 Program Counter (PC) is 11/12/13 bits wide, thus addressing the 2/4/8K program memory locations. The operation of Boot Program section and associated Boot Lock bits for software protection are described in detail in ”Self-Programming the Flash, ATmega48” on page 262 and ”Boot Loader Support – Read-While-Write Self-Programming, ATmega88 and ATmega168” on page 269. ”Memory Programming” on page 285 contains a detailed description on Flash Programming in SPI- or Parallel Programming mode.
Why pursue extraction despite these hurdles? For clients the benefits are real and measurable: timely recovery of firmware can reduce costly field downtime, enable security audits that identify and remediate vulnerabilities, permit lawful interoperability between legacy and new modules, and support product continuity when suppliers exit the market. For companies offering maintenance or reverse-engineering services, providing a verified, readable archive of a client’s embedded program can save months of re-engineering and preserve intellectual property value.
Importantly, extracting firmware from a locked device must be handled ethically and legally. Any work performed should have explicit authorization from the device owner, respect copyright and regulatory constraints, and avoid publishing methods that facilitate misuse. The value of Extract MCU ATmega168P Software lies in enabling responsible recovery, compliance, and product support — not in enabling unauthorized cloning or theft. When undertaken professionally, the process delivers tangible operational benefits while preserving legal and safety boundaries.

