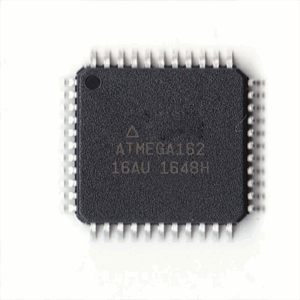
The demand to extract MCU ATMEGA162 code often arises in fields where legacy systems must be maintained, repaired, or analyzed. The ATMEGA162, a member of the Atmel AVR family, is a powerful 8-bit microcontroller (MCU) with Harvard architecture, dual UARTs, JTAG interface, and 16KB of in-system programmable flash memory. It is widely deployed in industrial controllers, automotive subsystems, communication equipment, and even consumer electronics, where stability and low power consumption are crucial.
When the firmware inside this chip becomes inaccessible due to secured lock bits or protected configurations, companies may face downtime or loss of valuable intellectual property. To recover or restore the internal binary, experts may attempt specialized procedures designed to overcome the chip’s hardware defenses.
Unlike simpler MCUs, the ATMEGA162 provides multiple levels of flash security. Once locked, direct readout of data, program, or eeprom contents via ISP or JTAG becomes impossible. The only way to obtain a dump of the heximal file is through advanced attack methodologies:
-
Decapsulation and microprobing: By physically removing the packaging, engineers can expose the microprocessor die and directly tap into internal buses. This is extremely delicate and requires cleanroom facilities.
-
Fault injection attacks: Carefully timed voltage or clock glitches may trick the MCU into bypassing its encrypted or locked states.
-
Side-channel analysis: Monitoring current fluctuations or electromagnetic emissions can help decode operations and reveal clues about the stored source code.
-
Reverse engineering the boot process: Exploiting weaknesses in bootloader or fuse bit configurations to regain limited memory access.
Each of these methods is complex, expensive, and often requires iterative experimentation. The process to crack, break, or hack an ATMEGA162 is not a simple duplication task but an involved reverse engineering effort.

Extract MCU ATMEGA162 Code from the microcontroller ATmega162 memory include flash and eeprom, reverse engineering microcontroller composition and delayer the MCU to get access to the inner security fuse and cut if off by focus ion beam;
Features
- High-performance, Low-power AVR® 8-bit Microcontroller
- Advanced RISC Architecture
– 131 Powerful Instructions – Most Single-clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplies
Non-volatile Program and Data Memories
– 16K Bytes of In-System Self-programmable Flash Endurance: 10,000 Write/Erase Cycles
– Optional Boot Code Section with Independent Lock Bits
In-System Programming by On-chip Boot Program
True Read-While-Write Operation
– 512 Bytes EEPROM
Endurance: 100,000 Write/Erase Cycles
– 1K Bytes Internal SRAM
– Up to 64K Bytes Optional External Memory Space
– Programming Lock for Software Security
JTAG (IEEE std. 1149.1 Compliant) Interface
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– Two 16-bit Timer/Counters with Separate Prescalers, Compare Modes, and Capture Modes
– Real Time Counter with Separate Oscillator
– Six PWM Channels
– Dual Programmable Serial USARTs
– Master/Slave SPI Serial Interface to read microcontroller atmega64 eeprom
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Five Sleep Modes: Idle, Power-save, Power-down, Standby, and Extended Standby I/O and Packages
– 35 Programmable I/O Lines
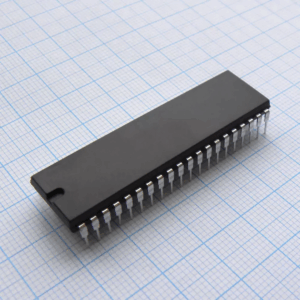
– 40-pin PDIP, 44-lead TQFP, and 44-pad MLF
Operating Voltages
– 1.8 – 5.5V for ATmega162V
– 2.7 – 5.5V for ATmega162
Speed Grades
– 0 – 8 MHz for ATmega162V (see Figure 113 on page 265)
– 0 – 16 MHz for ATmega162 (see Figure 114 on page 265)
The ATmega162 is a low-power CMOS 8-bit microcontroller based on the AVR enhanced RISC architecture. By executing powerful instructions in a single clock cycle, the ATmega162 achieves throughputs approaching 1 MIPS per MHz allowing the system designer to optimize power consumption versus processing speed.
Despite the difficulties, successfully extracting the program archive from this MCU opens significant opportunities. Engineers can clone or replicate the firmware for use in new production runs, duplicate hardware platforms without rewriting critical software, or restore functionality in obsolete products. A recovered binary also allows for copying and analysis of proprietary algorithms that may otherwise be lost.
One challenge unique to the ATMEGA162 is its robust protected memory design, which integrates fuse bits to configure bootloader sections, lock levels, and even disable debugging features. Once these security measures are enabled, only highly specialized chip-level attacks can reveal the underlying file system. This makes the extraction of firmware from a locked ATMEGA162 distinctly more difficult compared to simpler 8051-based MCUs.
In conclusion, the process to extract MCU ATMEGA162 code is a specialized and demanding undertaking. It combines hardware decapsulation, cryptographic decryption, and system-level reverse engineering to retrieve firmware archives from a secured and protected AVR chip. While the technical barriers are formidable, the successful recovery of such data ensures continuity of industrial operations and preservation of embedded knowledge.
