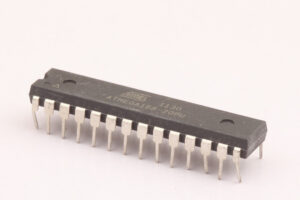
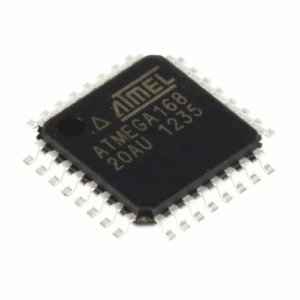
“Extract IC ATmega168 Code” captures a common need in embedded engineering: obtaining a copy of the firmware or binary archive from a device’s microcontroller for legitimate reasons such as device maintenance, interoperability, or legacy system restoration. The ATmega168, part of Microchip/Atmel’s AVR family, is a widely used 8-bit MCU featuring flash program memory, EEPROM, SRAM, and a rich peripheral set (timers, ADC, serial interfaces). It is commonly deployed in consumer electronics, hobbyist boards, instrumentation, low-power sensors, and certain industrial controllers where a compact, cost-effective microprocessor is required.

When attempting to recover or duplicate an ATmega168 program, engineers often confront the reality that many deployments enable lock bits or other protections, rendering the chip’s flash or EEPROM protected, locked, or otherwise secured. The desire to clone, replicate, or restore a program may stem from business continuity needs — for example, needing to recover a lost heximal file or to analyze a legacy archive to maintain devices still in the field.
Extract IC ATmega168 Code from its embedded flash memory, break mcu atmega168 security protection and then readout embedded heximal file from atmega168 flash and eeprom memory;

During interrupts and subroutine calls, the return address Program Counter (PC) is stored on the Stack. The Stack is effectively allocated in the general data SRAM, and consequently the Stack size is only limited by the total SRAM size and the usage of the SRAM. All user programs must initialize the SP in the Reset routine (before subroutines or interrupts are executed).
The Stack Pointer (SP) is read/write accessible in the I/O space. The data SRAM can easily be accessed through the five different addressing modes supported in the AVR architecture. The memory spaces in the AVR architecture are all linear and regular memory maps.
A flexible interrupt module has its control registers in the I/O space with an additional Global Interrupt Enable bit in the Status Register. All interrupts have a separate Interrupt Vector in the Interrupt Vector table. The interrupts have priority in accordance with their Interrupt Vector position. The lower the Interrupt Vector address, the higher the priority.
There are a few broad conceptual classes of activity related to extracting code from a secured MCU: non-invasive analysis, semi-invasive investigation, and invasive physical examination. Each class carries increasing technical complexity, cost, and risk to the target chip and its data. Non-invasive approaches rely on interfaces and visible behavior; semi-invasive methods interact with packaging surfaces; invasive methods may involve physical access to the silicon.
Regardless of approach, the central technical challenges are the same: extracting a reliable dump of the program memory without corrupting it, interpreting the raw binary into meaningful source code or disassembled logic, and dealing with any encryption, obfuscation, or integrity checks embedded by the original developer.
Practical difficulties in legitimate recovery efforts include small geometries and dense packaging that make probing fragile, limited on-chip resources that complicate memory mapping, and manufacturer-implemented lock mechanisms that prevent direct readout. Even when a binary file is obtained, further work is often required to decode and analyze the data — disassembly, symbolic reconstruction, and protocol inference — to reconstruct the original program behavior.
The I/O memory space contains 64 addresses for CPU peripheral functions as Control Registers, SPI, and other I/O functions. The I/O Memory can be accessed directly, or as the Data Space locations following those of the Register File, 0x20 – 0x5F. In addition, the ATmega48/88/168 has Extended I/O space from 0x60 – 0xFF in SRAM where only the ST/STS/STD and LD/LDS/LDD instructions.
The high-performance AVR ALU operates in direct connection with all the 32 general purpose working registers. Within a single clock cycle, arithmetic operations between general purpose registers or between a register and an immediate are executed. The ALU operations are divided into three main categories – arithmetic, logical, and bit-functions. Some implementations of the architecture also provide a powerful multiplier supporting both signed/unsigned multiplication and fractional format.

See the “Instruction Set” section for a detailed description. The Status Register contains information about the result of the most recently executed arithmetic instruction. This information can be used for altering program flow in order to perform conditional operations. Note that the Status Register is updated after all ALU operations, as specified in the Instruction Set Reference. This will in many cases remove the need for using the dedicated compare instructions, resulting in faster and more compact code. The Status Register is not automatically stored when entering an interrupt routine and restored when returning from an interrupt. This must be handled by software.
The Global Interrupt Enable bit must be set for the interrupts to be enabled. The individual interrupt enable control is then performed in separate control registers. If the Global Interrupt Enable Register is cleared, none of the interrupts are enabled independent of the individual interrupt enable settings. The I-bit is cleared by hardware after an interrupt has occurred, and is set by the RETI instruction to enable subsequent interrupts. The I-bit can also be set and cleared by the application with the SEI and CLI instructions, as described in the instruction set reference.
Beyond the technical hurdles are legal and ethical boundaries. Attempting to hack, crack, decrypt, or decapsulate a protected chip without explicit authorization can violate copyright, trade-secret, and anti-circumvention laws. For organizations needing a legitimate restore or duplicate, safer alternatives include contacting the chip or device vendor for support, seeking a license or cooperation agreement, or hiring accredited reverse-engineering professionals who operate under clear legal authorization.
In summary, Extract IC ATmega168 Code is a valid engineering concern — but one that sits at the intersection of hardware complexity, reverse engineering skill, and legal responsibility. When recovery of a secured firmware is required, prioritize authorized, ethical avenues and professional expertise rather than ad hoc attempts to break protections.
