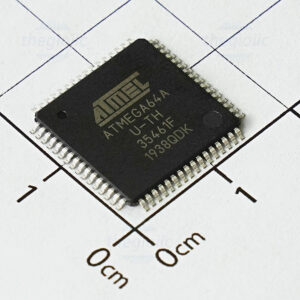
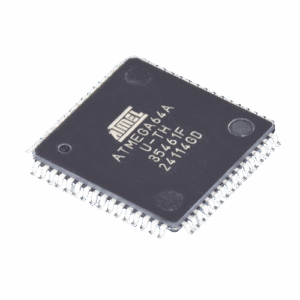
The phrase Read Microcontroller ATmega64A Heximal captures a common objective in embedded engineering: obtaining the stored program or binary representation (the “heximal” file) from an ATmega64A MCU for legitimate purposes such as archival, repair, or interoperability. The ATmega64A, part of the AVR family originally from Atmel and now supported by Microchip, is a widely used 8‑bit microcontroller with up to 64KB of in‑system programmable flash memory, EEPROM, SRAM, and a rich set of peripherals including timers, ADCs, UART, SPI, and I²C. Its combination of modest memory, low power and flexible I/O makes it suitable for consumer devices, industrial controllers, measurement instruments, hobbyist platforms, and certain automotive or appliance controllers.

Read Microcontroller ATmega64A Heximal needs to break avr mcu atmega64a protective system and extract secured source code from microprocessor flash and eeprom memory;
Problem Fix / Workaround
If ATmega64 is the only device in the scan chain, the problem is not visible.
Select the Device ID Register of the ATmega64 by issuing the IDCODE instruction or by entering the Test-Logic-Reset state of the TAP controller to read out the contents of its Device ID Register and possibly data from succeeding devices of the scan chain.
Issue the BYPASS instruction to the ATmega64 while reading the Device ID Registers of preceding devices of the boundary scan chain. If the Device IDs of all devices in the boundary scan chain must be captured simultaneously, the ATmega64 must be the fist device in the chain before Read Microcontroller.
When organizations talk about wanting to read an ATmega64A’s contents, related verbs and nouns commonly appear: crack / break / attack / decode / decapsulate / hack / decrypt / clone / copy / recover / replicate / duplicate /restore /reverse engineering, and words such as firmware / source code / binary / heximal / EEPROM / flash / program / memory / file / data / archive /MCU /chip /dump. These terms reflect a range of motivations — from lawful recovery of a lost firmware archive to concerns about unauthorized copying or intellectual property protection.

There are several legitimate reasons to seek a readout of a microcontroller’s flash program. Manufacturers and service providers often need to recover or restore firmware for legacy products when source code has been lost; system integrators may need to duplicate a program for authorized spare units; researchers and security teams may reverse engineer firmware to validate safety or to analyze vulnerabilities in order to fix them; and repair technicians may need to recover calibration data or configuration archives to return equipment to service.
- First Analog Comparator conversion may be delayed
If the device is powered by a slow rising VCC, the first Analog Comparator conversion will take longer than expected on some devices.
Problem Fix/Workaround
When the device has been powered or reset, disable then enable theAnalog Comparator before the first conversion.
- Interrupts may be lost when writing the timer registers in the asynchronous timer
If one of the timer registers which is synchronized to the asynchronous timer2 clock is written in the cycle before a overflow interrupt occurs, the interrupt may be lost.

Problem Fix/Workaround
Always check that the Timer2 Timer/Counter register, TCNT2, does not have the value 0xFF before writing the Timer2 Control Register, TCCR2, or Output Compare Register, OCR2;
- Stabilizing time needed when changing XDIV Register
After increasing the source clock frequency more than 2% with settings in the XDIV register, the device may execute some of the subsequent instructions incorrectly.
Problem Fix / Workaround
The NOP instruction will always be executed correctly also right after a frequency change. Thus, the next 8 instructions after the change should be NOP instructions. To ensure this, follow this procedure:
1.Clear the I bit in the SREG Register.
2.Set the new pre-scaling factor in XDIV register.
3.Execute 8 NOP instructions
4.Set the I bit in SREG
This will ensure that all subsequent instructions will execute correctly.
However, practical and legal obstacles make such tasks nontrivial. Modern devices commonly employ lock‑bit protections, encrypted storage, and secure boot mechanisms that render flash contents protected or locked against standard readout. These protections exist to safeguard intellectual property, user data, and device integrity. From a practical standpoint, small package sizes, multilayer PCBs, and minimal exposed debug interfaces complicate access. From a legal and ethical standpoint, attempting to crack or clone protected firmware without explicit authorization can violate copyright, licensing agreements, and local laws.
Because of these constraints, the appropriate course for legitimate needs is to pursue lawful, documented paths: request firmware or recovery assistance from the original equipment manufacturer, obtain explicit authorization from the device owner, use published update or recovery procedures, or engage qualified, authorized service providers. When reverse engineering is performed for compatibility, archival, or security research, it should be done transparently and ethically, with due attention to intellectual property rights and applicable laws.

In summary, Read Microcontroller ATmega64A Heximal defines an important capability for maintenance, preservation, and analysis of embedded systems. The ATmega64A’s widespread deployment across industries underscores the value of responsibly handling firmware archives. Yet the combination of technical protections and legal considerations makes clear that any effort to access protected program memory must proceed through authorized, non‑invasive, and lawful channels.
