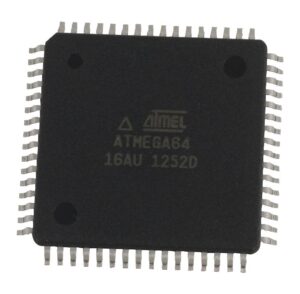
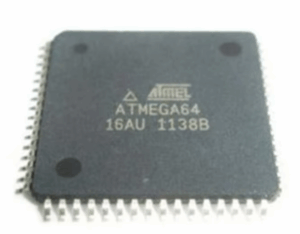
When engineers or researchers aim to read microcontroller ATMEGA64 EEPROM, they enter into the complex field of chip-level reverse engineering and firmware recovery. The ATMEGA64, designed by Atmel (now Microchip), is a high-performance 8-bit AVR microcontroller offering 64KB of in-system programmable flash memory, 4KB of EEPROM, and 2KB of SRAM. With advanced peripheral integration, this MCU is widely deployed in aerospace systems, automotive electronics, medical devices, industrial controllers, and communication equipment where both reliability and security are paramount.
The EEPROM in the ATMEGA64 often stores configuration parameters, calibration values, or small but critical segments of program data. In secured applications, these EEPROM contents may also hold encryption keys or unique identifiers essential to the system’s integrity. Extracting this binary or heximal file becomes extremely valuable when attempting to recover, duplicate, or restore a legacy embedded system, or when an organization requires replication of existing hardware without redesigning from scratch.
Challenges in Accessing a Secured ATMEGA64
The ATMEGA64 is equipped with lock bits and fuse settings that prevent unauthorized copy or dump operations of both firmware and EEPROM contents. Once these protections are activated, direct access to the internal memory is blocked through conventional programming interfaces such as ISP (In-System Programming) or JTAG.
To crack, break, or hack this level of security requires advanced attack techniques, including:
-
Decapsulation – Removing the protective epoxy package to expose the silicon die, allowing physical probing of internal circuits.
-
Fault injection – Using voltage or clock glitches to force the microcontroller into bypassing its secured state.
-
Side-channel analysis – Measuring power fluctuations or electromagnetic emissions to indirectly decode or decrypt internal operations.
-
Firmware emulation and reverse engineering – Reconstructing missing portions of binary or data archive from partially extracted program files.
These processes are not only technically demanding but also require specialized laboratory equipment, such as scanning electron microscopes, microprobing stations, and precision laser tools.

Industrial Importance of EEPROM Extraction
The demand to read microcontroller ATMEGA64 EEPROM often arises in scenarios where devices are long out of production, and original source code or development files have been lost. For example:
-
Aerospace and defense: Recovering firmware from protected flight control systems or mission-critical devices.
-
Automotive: Extracting calibration data or diagnostic logic from obsolete ECUs.
-
Medical electronics: Restoring unique program settings from life-support or diagnostic equipment.
-
Industrial controllers: Replicating locked hardware modules to ensure continuity in production lines.
Why the ATMEGA64 is Difficult to Break
Compared to smaller MCUs, the ATMEGA64 integrates stronger memory protection mechanisms and more complex program structures. Its encrypted bootloader options and fuse-controlled lock bits make cloning or copying especially resistant to direct approaches. Even if the flash memory is eventually accessed, correlating the binary dump with EEPROM configuration often requires deep reverse engineering to fully reconstruct the system’s behavior.
Read Microcontroller ATMEGA64 Eeprom content from its flash memory needs to disable the tamper resistance system by MCU Cracking method which include power glitch and physical intrution;

The ATmega64 provides the following features: 64K bytes of In-System Programmable Flash with Read-While-Write capabilities, 2K bytes EEPROM, 4K bytes SRAM, 53 general purpose I/O lines, 32 general purpose working registers, Real Time Counter (RTC), four flexible Timer/Counters with compare modes and PWM, two USARTs, a byte oriented Two-wire Serial Interface, an 8-channel, 10-bit ADC with optional differential input stage with programmable gain, programmable Watchdog Timer with internal Oscillator, an SPI serial port, IEEE std. 1149.1 compliant JTAG test interface, also used for accessing the On-chip Debug system and programming, and six software selectable power saving modes when extract mcu attiny13v hex.
The Idle mode stops the CPU while allowing the SRAM, Timer/Counters, SPI port, and interrupt system to continue functioning. The Power down mode saves the register contents but freezes the Oscillator, disabling all other chip functions until the next interrupt or Hardware Reset.
In Power-save mode, the asynchronous timer continues to run, allowing the user to maintain a timer base while the rest of the device is sleeping. The ADC Noise Reduction mode stops the CPU and all I/O modules except asynchronous timer and ADC, to minimize switching noise during ADC conversions.
In Standby mode, the crystal/resonator Oscillator is running while the rest of the device is sleeping. This allows very fast start-up combined with low power consumption. In Extended Standby mode, both the main Oscillator and the asynchronous timer continue to run after extract attiny15 software.
The device is manufactured using Atmel’s high-density non-volatile memory technology. The On-chip ISP Flash allows the program memory to be reprogrammed In-System through an SPI serial interface, by a conventional non-volatile memory programmer, or by an On-chip Boot program running on the AVR core. The Boot Program can use any interface to download the Application Program in the Application Flash memory.
Software in the Boot Flash section will continue to run while the Application Flash section is updated, providing true Read-While-Write operation. By combining an 8-bit RISC CPU with In-System Self-Programmable Flash on a monolithic chip, the Atmel ATmega64 is a powerful microcontroller that provides a highly-flexible and cost-effective solution to many embedded control applications.
The ATmega64 AVR is supported with a full suite of program and system development tools including: C compilers, macro assemblers, program debugger/simulators, In-Circuit Emulators, and evaluation kits. The ATmega64 is a highly complex microcontroller where the number of I/O locations supersedes the 64 I/O location reserved in the AVR instruction set.
To ensure backward compatibility with the ATmega103, all I/O locations present in ATmega103 have the same location in ATmega64. Most additional I/O locations are added in an Extended I/O space starting from 0x60 to 0xFF (i.e., in the ATmega103 internal RAM space).
These location can be reached by using LD/LDS/LDD and ST/STS/STD instructions only, not by using IN and OUT instructions. The relocation of the internal RAM space may still be a problem for ATmega103 users. Also, the increased number of Interrupt Vectors might be a problem if the code uses absolute addresses. To solve these problems, an ATmega103 compatibility mode can be selected by programming the fuse M103C when Read Microcontroller.
In this mode, none of the functions in the Extended I/O space are in use, so the internal RAM is located as in ATmega103. Also, the extended Interrupt Vectors are removed. The ATmega64 is 100% pin compatible with ATmega103, and can replace the ATmega103 on current printed circuit boards. The application notes “Replacing ATmega103 by ATmega128” and “Migration between ATmega64 and ATmega128” describes what the user should be aware of replacing the ATmega103 by an ATmega128 or ATmega64.
The ability to read microcontroller ATMEGA64 EEPROM from a locked or protected chip is not a simple task of copying data. It involves a multi-layered approach that combines decapsulation, fault injection, side-channel decoding, and expert reverse engineering to recover and restore valuable firmware archives. This makes the ATMEGA64 both a robust choice for industry applications and a formidable target for those seeking to replicate, duplicate, or clone its secured contents.
