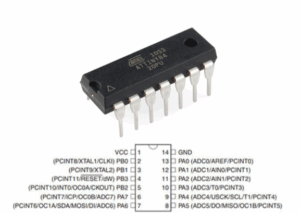
To Read IC ATtiny84 Firmware is to engage in a targeted, professional process: extracting the compiled program image and associated data from a tiny, resource-constrained microcontroller so that organizations can recover, maintain, or audit embedded systems. The ATtiny84 is a compact AVR-class MCU valued for its efficient power profile, versatile I/O, and modest on-chip flash and EEPROM. That combination makes it a frequent choice for portable interfaces, LED drivers, small measurement devices, sensor controllers, and compact consumer products where space and power are at a premium.
The firmware stored in an ATtiny84’s flash often contains more than simple control loops — calibration tables, device-specific parameters, communication logic, and proprietary program routines are commonly embedded alongside persistent configuration in EEPROM. When a company loses source repositories, needs to restore a corrupted update, or must validate the behavior of fielded hardware, obtaining a binary dump of that flash becomes essential. A recovered hex or binary file then serves as the archive engineers analyze to rebuild, validate, or reproduce product behavior.
Read IC ATtiny84 Firmware out from its memory needs to unlock microcontroller attiny84 flash memory and then break MCU Attiny84 protection;

The ATtiny13A is a low-power CMOS 8-bit microcontroller based on the AVR enhanced RISC architecture. By executing powerful instructions in a single clock cycle, the ATtiny13A achieves throughputs approaching 1 MIPS per MHz allowing the system designer to optimize power consumption versus processing speed.
The AVR core combines a rich instruction set with 32 general purpose working registers. All 32 registers are directly connected to the Arithmetic Logic Unit (ALU), allowing two independent registers to be accessed in one single instruction executed in one clock cycle. The resulting architecture is more code efficient while achieving throughputs up to ten times faster than conventional CISC microcontrollers.
Because many vendors set their devices to a protected or locked state to prevent unauthorized copying, the task of gaining access to the program image requires careful, authorized handling. Discussions around this work may mention terms like reverse engineering, decoding, or recovery, but ethical practice avoids public instructions on how to bypass protection. The focus is on non-destructive retrieval and interpretation: producing a faithful program dump and then using skilled analysis to translate machine code into meaningful, actionable insight without facilitating piracy or unlawful cloning.

The ATtiny84’s feature set explains its common deployments. With useful analog peripherals, timers, and serial interfaces in a small package, it suits battery-powered sensors, wearable controls, simple user-interface panels, and compact automation modules. Its limited memory footprint often leads to highly optimized binaries that are dense and challenging to interpret — a recovered file is usually only the first step; reconstructing program logic or rebuilding missing source code requires expertise in AVR instruction sets and careful forensic analysis.
The ATtiny13A provides the following features: 1K byte of In-System Programmable Flash, 64 bytes EEPROM, 64 bytes SRAM, 6 general purpose I/O lines, 32 general purpose working registers, one 8-bit Timer/Counter with compare modes, Internal and External Interrupts, a 4-channel, 10-bit ADC, a programmable Watchdog Timer with internal Oscillator, and three software selectable power saving modes. The Idle mode stops the CPU while allowing the SRAM, Timer/Counter, ADC, Analog Comparator, and Interrupt system to continue functioning.
The Power-down mode saves the register contents, disabling all chip functions until the next Interrupt or Hardware Reset. The ADC Noise Reduction mode stops the CPU and all I/O modules except ADC, to minimize switching noise during ADC conversions.
The device is manufactured using Atmel’s high density non-volatile memory technology. The On-chip ISP Flash allows the Program memory to be re-programmed In-System through an SPI serial interface, by a conventional non-volatile memory programmer or by an On-chip boot code running on the AVR core.
The ATtiny13A AVR is supported with a full suite of program and system development tools including: C Compilers, Macro Assemblers, Program Debugger/Simulators, and Evaluation kits.
A comprehensive set of drivers, application notes, data sheets and descriptions on development tools are available for download at http://www.atmel.com/avr. This documentation contains simple code examples that briefly show how to use various parts of the device to extract mcu attiny44 code.
These code examples assume that the part specific header file is included before compilation. Be aware that not all C compiler vendors include bit definitions in the header files and interrupt handling in C is compiler dependent. Please confirm with the C compiler documentation for more details. Reliability Qualification results show that the projected data retention failure rate is much less than 1 PPM over 20 years at 85°C or 100 years at 25⋅C.
Practical difficulties in working with protected ATtiny84 devices are both physical and analytical. Small packages and crowded PCB layouts may hide debug contacts, complicating non-invasive readout and increasing risk of damaging the board or corrupting EEPROM data. Logical protections such as lock bits are explicitly designed to refuse standard reads, so authorized recovery efforts must respect legal and contractual boundaries. Even after a successful read, the resulting binary lacks comments and symbols; making it useful typically involves methodical reverse engineering to infer data structures, protocol behavior, and control flow.
Why undertake this work? For clients, the benefits are concrete: restoring a verified firmware archive can dramatically reduce field downtime, enable prompt repairs, and preserve product continuity when vendors discontinue support. Security teams gain the ability to audit legacy code for vulnerabilities; manufacturers can reproduce or restore units lawfully under proper authorization; and organizations gain a managed archive that safeguards intellectual property and supports compliance efforts.
In short, Read IC ATtiny84 Firmware is a specialized, high-value service that balances technical skill with legal and ethical responsibility. Done correctly, it turns an inaccessible, locked program image into a controlled, analyzable asset that supports maintenance, safety, and long-term product value for the client.

