Read IC ATtiny45 Heximal refers to the controlled, professional process of extracting a device’s binary or heximal program image from a secured, protected, or even encrypted microcontroller. Although the ATtiny45 belongs to the same AVR family as the ATtiny25, it offers a slightly larger flash memory, more flexible peripheral features, and a compact design that makes it popular across a variety of industries. Because of this, essential firmware, calibration data, and small but critical control programs are often stored directly inside its on-chip flash and EEPROM. When these internal resources become inaccessible due to lost repositories, expired vendor support, or locked production devices, organizations may need a legitimate method to extract, recover, or restore the embedded logic.

The ATtiny45 is commonly deployed in battery-powered consumer electronics, small IoT sensors, LED lighting systems, control modules in appliances, automotive accessories, industrial signal converters, and smart actuators. Its efficiency, tiny footprint, and reliable architecture help designers implement everything from simple timing functions to more refined data processing tasks. In many cases, the microcontroller becomes the heart of a product, and its memory contains configuration tables, encrypted identifiers, or calibration archives that are impossible to rebuild without direct access to the chip.
Read IC ATtiny45 Heximal needs to unlock attiny45 microcontroller protective system and break tamper resistance of mcu attiny45 by focus ion beam technique;

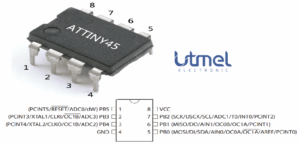
Port B is a 6-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port B output buffers have symmetrical drive characteristics with both high sink and source capability.
As inputs, Port B pins that are externally pulled low will source current if the pull-up resistors are activated. The Port B pins are tri-stated when a reset condition becomes active, even if the clock is not running.
Reset input. A low level on this pin for longer than the minimum pulse length will generate a reset, even if the clock is not running. The minimum pulse length is given in Table 23-3 on page 170. Shorter pulses are not guaranteed to generate a reset.
- For compatibility with future devices, reserved bits should be written to zero if accessed. Reserved I/O memory addresses should never be written.
- I/O Registers within the address range 0x00 – 0x1F are directly bit-accessible using the SBI and CBI instructions. In these registers, the value of single bits can be checked by using the SBIS and SBIC instructions.
- Some of the Status Flags are cleared by writing a logical one to them by reading mcu attiny45v flash memory program. Note that, unlike most other AVRs, the CBI and SBI instructions will only operation the specified bit, and can therefore be used on registers containing such Status Flags. The CBI and SBI instructions work with registers 0x00 to 0x1F only.
The ATTINY45 provides the following standard features:

20K bytes of Flash, 256-bytes of RAM, 32 I/O lines, three 16-bit timer/counters, a six-vector two-level interrupt architecture, a full duplex serial port, on-chip oscillator, and clock circuitry. In addition, the AT89C55 is designed with static logic for operation down to zero frequency and supports two software selectable power saving modes.
However, reading a protected ATtiny45 is not always straightforward. Modern devices often utilize locked fuse settings that prevent standard interfaces from reading flash or EEPROM. Engineers may encounter blocked programming modes, missing pads on the PCB, or deeply embedded chips that cannot be accessed without care. Recovering a binary, dump, or heximal file from such a device may require deep understanding of embedded hardware behavior and precise, responsible methodologies that avoid damaging the chip or corrupting its internal archive. These tasks fall under the larger umbrella of controlled reverse engineering, which here is applied not for unauthorized duplication but for legal and documented system restoration.

Why would clients need this service? The reasons are practical, often urgent, and entirely legitimate. A company might need to open the firmware to restore production after a system failure. Another may require a clean extract of an older program to reproduce a discontinued product module that remains essential to service equipment. Others may need to validate their source code against what is actually deployed in the field, especially for compliance or safety audits. In each scenario, the ability to recover a locked program offers clear business value.
The Idle Mode stops the CPU while allowing the RAM, timer/counters, serial port, and interrupt system to continue functioning. The Power Down Mode saves the RAM contents but freezes the oscillator, disabling all other chip functions until the next hardware reset. The low-voltage option saves power and operates with a 2.7-volt power supply.
For clients, the benefit is not only gaining access to the lost program but also ensuring that knowledge embedded inside the microprocessor is preserved as a long-term archive. This significantly reduces downtime, enables manufacturing continuity, and safeguards intellectual property. A verified, readable flash image becomes an asset—one that ensures their devices remain maintainable and reproducible across the entire product lifecycle.
In summary, Read IC ATtiny45 Heximal represents a highly specialized service that blends hardware insight, responsible reverse engineering, and disciplined data recovery practices. When executed properly, it transforms a sealed, inaccessible program into a secure, recoverable resource that clients can reuse, document, or redeploy with confidence.
