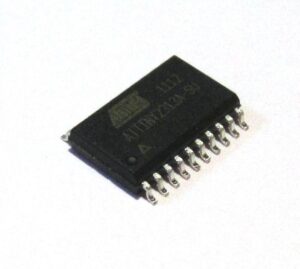
The process to extract MCU ATtiny2313A heximal data is a highly technical and carefully controlled engineering task. The ATtiny2313A microcontroller from Microchip is a widely deployed compact MCU featuring low power consumption, integrated flash memory, internal EEPROM, UART, timers, and flexible I/O capability. Because of its balance between cost and capability, it is found in diverse applications such as industrial automation controllers, lighting systems, small motor drivers, smart locks, access control electronics, laboratory equipment, and legacy programmable modules.

In many real-world scenarios, the original firmware, source code, or archived program file may be missing due to discontinued R&D departments, expired suppliers, lost development environments, or damaged storage servers. When that happens, the only practical way to continue supporting an existing product line is to recover, open, or restore the embedded binary dump directly from the chip. This requires advanced knowledge of reverse engineering, hardware analysis, and secure readout methodology.
Extract MCU ATtiny2313A Heximal from flash and eeprom memory needs to unlock attiny4313a processor protective fuse bit and recover secured firmware heximal to new microcontroller attiny4313a;

Port B is an 8-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port B output buffers have symmetrical drive characteristics with both high sink and source capability.
As inputs, Port B pins that are externally pulled low will source current if the pull-up resistors are activated. The Port B pins are tri-stated when a reset condition becomes active, even if the clock is not running.
Port D is a 7-bit bi-directional I/O port with internal pull-up resistors (selected for each bit). The Port D output buffers have symmetrical drive characteristics with both high sink and source capability. As inputs, Port D pins that are externally pulled low will source current if the pull-up resistors are activated. The Port D pins are tri-stated when a reset condition becomes active, even if the clock is not running.
Reset input. A low level on this pin for longer than the minimum pulse length will generate a reset, even if the clock is not running and provided that the reset pin has not been disabled. The minimum pulse length is given in Table 21-3 on page 198. Shorter pulses are not guaranteed to generate a reset.

The Reset Input is an alternate function for PA2 and dW. The reset pin can also be used as a (weak) I/O pin. The ATtiny2313A/4313 is a low-power CMOS 8-bit microcontroller based on the AVR enhanced RISC architecture. By executing powerful instructions in a single clock cycle, the ATtiny2313A/4313 achieves throughputs approaching 1 MIPS per MHz allowing the system designer to optimize power consumption versus processing speed.
The AVR core combines a rich instruction set with 32 general purpose working registers. All the 32 registers are directly connected to the Arithmetic Logic Unit (ALU), allowing two independent registers to be accessed in one single instruction executed in one clock cycle.
The resulting architecture is more code efficient while achieving throughputs up to ten times faster than conventional CISC microcontrollers.
However, extracting binary, heximal, or configuration data from a secured ATtiny2313A is far from trivial. The chip may have been intentionally protected, locked, or encrypted through fuse bits to prevent unauthorized access to the internal firmware. These protection mechanisms are designed to block low-level reading of EEPROM, flash, or memory registers. Attempts to bypass security without experience may permanently damage the chip or destroy its file contents.
Our specialized extraction service is built around precision and safety. Instead of brute-force hacking, we follow a controlled, step-based approach to ensure that the data, firmware, or archived program can be extracted without corrupting the stored information. The final output is typically provided in multiple formats including hex, raw binary, and readable archive form, allowing engineers to study, modify, duplicate, or redeploy the recovered program for production or maintenance purposes.

The meaning and value behind this process is clear: retrieving firmware from a protected microcontroller allows companies to maintain product continuity, avoid expensive redesigns, support replacement units, and extend life-cycle management of machinery or consumer devices. By providing secure and professional extraction, we help transform a locked embedded system into usable engineering knowledge, protecting both past investment and future product strategy.

